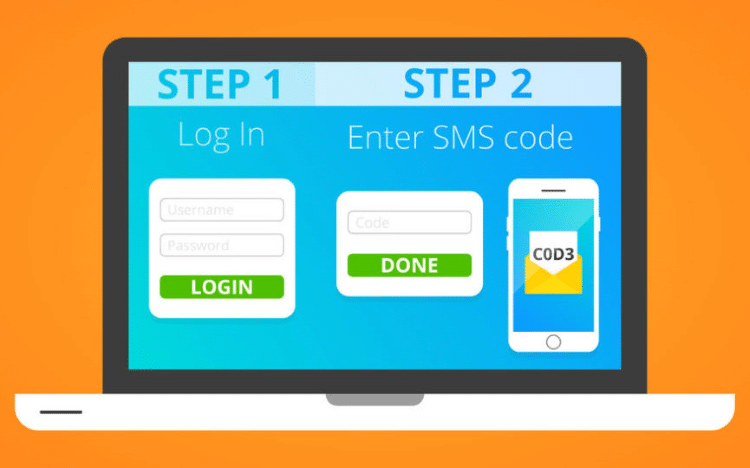
I’m all about 2-factor authentication, but what I’ve discovered recently has made me more cautious about how I set it up…
Avoid using codes texted to your phone for 2-factor authentication.
Using your cell number is one of the most common ways to set up 2-factor authentication. Everyone has used a code texted to their phone to get access to a site or reset a password… yet we are discovering risks with this option.
When you lose control over your cell number — maybe it’s hijacked by fraudsters, you get separated or divorced, late on your phone bill payments, or you switch carriers and your old carrier rehashes your number — whoever inherits the number can become YOU in a lot of places online. Countless sites still allow users to reset passwords with nothing more than a one-time code texted to a cell number on the account. Losing control of your cell number is as dangerous as a hacker getting their hands on your Social Security Number!
Here’s a quick story to highlight the danger of this:
“A while ago I bought a new phone and got a new number. I went on Yahoo! mail and typed in the number in the login. It asked me if I wanted to receive an SMS to gain access. I said yes, and it sent me an access code via SMS. I typed the code I received. I was surprised that I didn’t access my own email, yet the email of the previous number’s owner.
Yahoo! didn’t even ask me to type the email address or the first and last name. It merely sent me the SMS, I typed the code I received and it gave me access to the email of my number’s PREVIOUS OWNER. This seriously needs to be revised. At minimum Yahoo! should ask me to type the email address or my first and last name before sending me an SMS which contains an access code.”
You can’t avoid this danger on some sites, yet if you do have an option to choose how to set up your 2-factor authentication, we recommend using these methods:
- Google Authenticator (App)
- LastPass Authenticator (App)
- Yubico “Yubi Key” Authenticator Key (Hardware)
Apps do an excellent job with secure 2-factor, yet for those of you that might not have access to your phone or want physical security, a 2FA hardware key is a great option. Personally, I use both. If you have any questions, reach out. I’m happy to help anyone.
Stay safe out there,
Randy Sklar